Encryption and Security
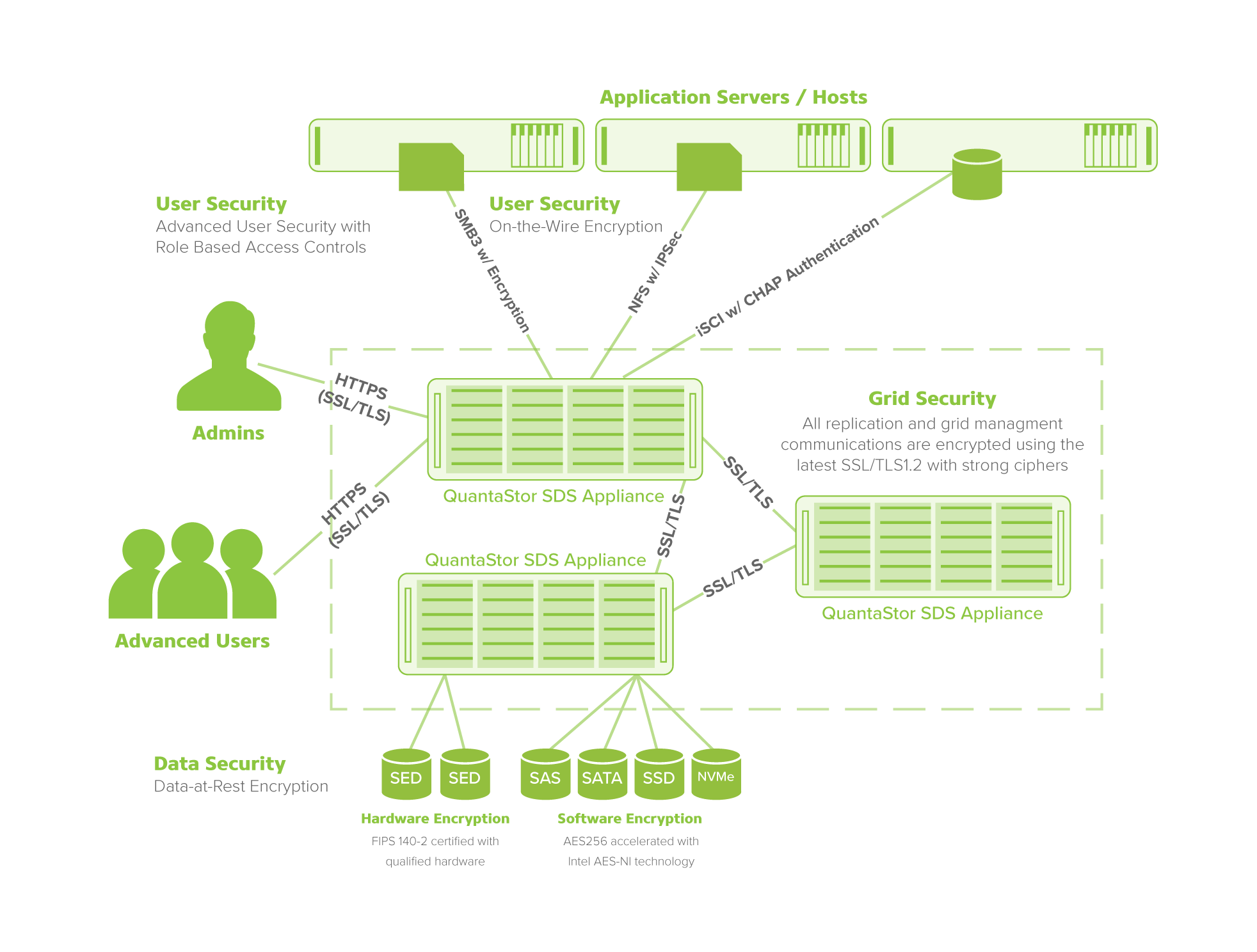
Maintain secure systems with multi-layer data protection on-the-wire and at-rest for enterprise and cloud storage deployments.
Combining protocol-level encryption with SMB, IPsec, and HTTPS across any storage grid, hardware and software disk drive encryption with Intel AES-NI technology and advanced user security featuring role-based access controls, QuantaStor end-to-end security is ideal for a variety of industry applications.
Security Model Features
Security Policy Enforcement
HIPAA and CJIS compliant password and security policy enforcement is built into the platform, making it easy to ensure compliance to government mandated security standards.
User Security
QuantaStor goes beyond basic Role Based Access Control (RBAC) with Advanced User Security by masking user permissions and allowing administrators to grant permissions for users at the storage object level, to all objects in the user's associated cloud(s) or to the entire storage system.
Client Security
For data on-the-wire, QuantaStor provides encryption via SMB3, IPSec, and HTTPS. For iSCSI storage, QuantaStor uses Challenge-Handshake Authentication Protocol (CHAP) supporting CHAP for storage volumes, user levels and storage clouds providing easier management and SAN security.
Data Security
For data-at-rest, QuantaStor features “one-click” full drive software encryption with Intel AES-NI technology and FIPS 140-2 self-encrypting drive support with certified hardware.
Data Shredding
Delete storage pools with device formatting using data shredding options including the 4-pass DoD 5220 22-M section 8-306 procedure, 4-pass NNSA Policy Letter NAP-14.1-C procedure, and the US Army AR380-19 method. Shredding is done at a block level on each disk device and is done concurrently across all disks in the storage pool. Enabled encryption keys can also be shredded.
Grid Security
All data replication and storage grid management communications are encrypted using SSL/TLS 1.2 with strong ciphers.